THERE is a delightfully simple way to explain the process by which certain types of problems are solved. If you have ever tried to solve a maze and reached a blocked wall, you would know that the next step in finding a solution would be to undo the last move, take the other turn, and explore that section of the maze. When attempting to solve a crossword, you may do something similar if an incorrect word choice is made. When you discover the mistake, you progressively undo the last guess, then explore another word that fits into the space available. What do games have to do with computing and with ICT? Plenty!
Certain computing problems require the same thinking. If you reach a point where progress is not possible, you undo the last move, effectively taking a step backward, then try another option until you have solved the problem. Sounds simple, right?
This was effectively the explanation shared with a news reporter this week, who inquired into the options for discovering the source of yet another fake story circulating via social media. Although such fake stories are concocted to stoke the flames of manufactured outrage, the principle is the same. Recursively following the trail of the previous sender should eventually lead to the source of the story, unless a sophisticated set of countermeasures are used to avoid detection.
Effective digital security requires that the origin and integrity of a message should not be subverted. Effectively, nothing that you say or type may be abused to suggest a different meaning. Equally, you would be unable to disassociate yourself from what you have indeed said or sent. If doubt exists, then you should be asking yourself what measures could be taken to protect the authenticity and reliability of your own messages.
To share your views, contact the author at: www.datashore.net or via The Voice.
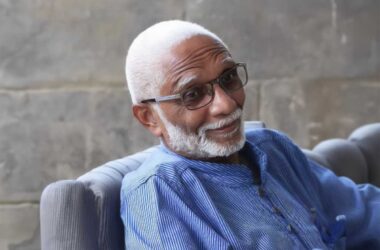
About the Author
Dr. Lyndell St. Ville is an ICT Consultant based in Saint Lucia. His expertise includes systems analysis, design, and capacity building.