THE recent spate of break-ins, robberies, and hold-ups, especially those targeting schools, has been alarming. Some of those attacks displayed a surprising degree of determination in their vicious operation, taking place under the cover of darkness, inclement weather, or even broad daylight! The fact that criminals are willing to risk life and limb in conducting their attacks suggests a new desperation and motivation that must be countered by intelligent preparation.
The increasing trend of this activity, where schools are targets for criminals, shows little sign of reversal. There was barely one week between celebrating World Teachers’ Day and another attack on a school. These attacks suggest that criminals recognise our increased use of ICT in schools, and unfortunately, consider these a likely target. As our schools become more ICT-based, there is a further risk of criminal activity and break-ins. Part of the solution to the problem is to reduce the temptation to steal and dispose of these items with such impunity. Effectively, to lessen the appeal of the ICT equipment in schools needed to mould the minds of the nations’ students.
Using technology to help with this problem, some options are to:
* Deploy a CCTV camera network to monitor school property;
* Maintain an asset register to identify the equipment at risk;
* Setup monitoring systems to raise the alert if items are removed.
A network of cameras improves the remote monitoring of the property, and provides useful evidence to further support police action. An equipment register is not only good practice, but it provides the means to trace stolen items and identify the perpetrators. A monitoring system may be configured to detect when an item has been removed, and trigger an alarm.
Many types of ICT equipment are internally tagged with unique labels and serial numbers to help with identification and asset management. For example, if you dial the sequence *#06# on your mobile phone, you should see the unique IMEI number. Other devices including laptops and tablet computers, are helpfully tagged with serial numbers and a MAC address. Armed with such information, the authorities may eventually identify stolen equipment.
From the comfort of your home, it is also possible to display a customised message on the screen of misplaced phones, to remotely lock missing devices, or to monitor the device location on a map. These are useful anti-theft features, which should cause criminals and others trading in stolen items, to have sleepless nights. If we took the time to register our equipment, then we could turn the tide on the criminals, and use the stolen goods to track them down. That would be poetic justice.
To share your views, contact the author at: www.datashore.net or via The VOICE.
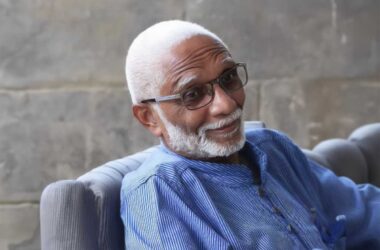
About the Author
Dr.Lyndell St. Ville is an ICT Consultant based in Saint Lucia. His expertise includes systems analysis and design.