IN a stunning blow to information security which will cause eyes and heads to roll, the Panamanian law-firm Mossack Fonseca has been hit by damming allegations of wrong-doing, and a breach in their information security. A stash of leaked data, comprising over 11 million files, have provided a treasure trove for journalists, financial and legal experts, and information analysts alike. Reports from the International Consortium of Investigative Journalists, in a breathtaking exposé, reveal how these secret files were obtained and processed. The affected law firm, unsurprisingly, intends to ensure that the “guilty parties are brought to justice”. At this stage, we can expect the investigative authorities to comb through a mountain of data to untangle the leads arising from this case.
You might probably be wondering how something like this could happen. Assuming that your computing system is protected by passwords, firewalls, and other security devices, how could someone defeat your high-priced security system? The answer is simple. Sometimes, the fault lies not with the technology, but with us, the owners. Although underlying technology is secure, the implementation may contain a flaw that allows an attacker to break through the veil of security.
Have you ever typed your password while your fingers were greasy? Someone looking at your keyboard could guess which keys correspond to your password. That technique works on tablet computers and mobile phones too. Based on this leaked information, an attacker could guess your password, defeating the otherwise good security.
Some other examples of information leakage:
* A chatty person talking on the phone in a careless manner;
* Posting personal details and pictures on social media;
* A sales agent loudly repeating your credit card details;
* Using an unknown computer or WIFI network.
Rest assured, this is a very short list. At a hotel some time ago, I received a handwritten note on a scrap of paper, from the front desk. The back of that reused sheet of paper contained a list of guests staying at the hotel, in a clear breach of security of those guests!
In the wake of the Panama Papers, we should expect that banks, credit unions, legal firms, financial authorities, and agencies storing sensitive information should take information security more seriously. Let’s face it. When our digital cameras, word processors, and photocopiers may be secretly storing sensitive information about us, perhaps we should all review our security practices.
—
To share your timely views, contact the author at: www.datashore.net or via The VOICE.
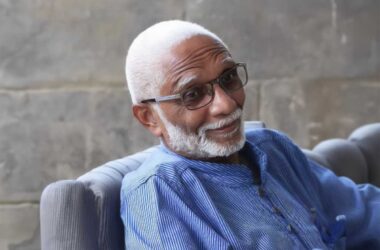
About the Author
Dr. Lyndell St. Ville is an ICT Consultant based in Saint Lucia. He builds capacity and advises on data management, information governance, and the safe use of technology.